More than 140 million accounts were compromised after the massive leak of users and passwords, impacting people around the world and covering online services from the most diverse sectors.The finding was made by cybersecurity researcher JeremiahFowler, who detailed the magnitude and scope of the exposure in a report published on ExpressVPN.
The discovery of the exposed database revealed an alarming volume of sensitive information.According to Fowler, the database contained 149,404,754 unique logins and passwords in a 96 GB file with no password protection or encryption.A preliminary review showed thousands of documents with emails, usernames, passwords and URL links to access or authorize accounts.
The researcher himself noted: “This is not the first data set of this type that I have discovered and it only highlights the global threat posed by credential-stealing malware.”Fowler stressed that stolen information is often stored in cloud repositories, and that not even cybercriminals are exempt from data breaches.

In this case, the database was publicly accessible, allowing anyone who found it to potentially access the credentials of millions of users.
The magnitude of the incident lies not only in the number of compromised accounts, but also in the diversity of services involved.Among the exposed data were credentials from social networks such as Facebook, Instagram, TikTok and X, as well as dating sites and applications.Even OnlyFans accounts appeared, including login paths for both creators and customers.
Fowler also identified a significant number of credentials associated with streaming and entertainment services, such as Netflix, HBOmax, DisneyPlus and Roblox.The impact extended to financial accounts, cryptocurrency wallets, trading platforms, and bank and credit card access data, according to the sample of records that the researcher reviewed.
Among the estimated figures, there are 48 million Gmail accounts, 4 million Yahoo accounts, 1.5 million Outlook accounts, 900 thousand iCloud accounts and 1.4 million.edu domains.Regarding social and entertainment platforms, 17 million Facebook accounts, 6.5 million Instagram accounts, 780 thousand TikTok accounts, 3.4 million Netflix accounts, 100 thousand OnlyFans accounts and 420 thousand Binance accounts were detected.
One of the aspects that generated the most concern in the analysis was the appearance of credentials linked to .gov domains from numerous countries.Fowler noted: “While not all government-linked accounts grant access to sensitive systems, even limited access could have serious consequences depending on the role and permissions of the compromised user.”
The exposure of these government credentials opens the door to selective phishing campaigns, identity theft or possible access to official networks.As the researcher warns, the risk to national and public security increases if the credentials fall into the wrong hands.

The investigation revealed that the database had no information that would allow it to identify its owner.Therefore, Fowler reported the situation directly to the hosting provider through an online abuse form.
The initial response was that the IP did not belong to the parent company, but to an independent subsidiary that still used the name of the parent organization.
Fowler had to insist for almost a month and after several attempts, the hosting was finally suspended and the millions of stolen credentials were no longer publicly accessible.
The provider did not offer details about who was behind the database or whether the information was used for criminal or investigative purposes.It is also not known how long the database was available before it was reported, nor if other actors accessed it.

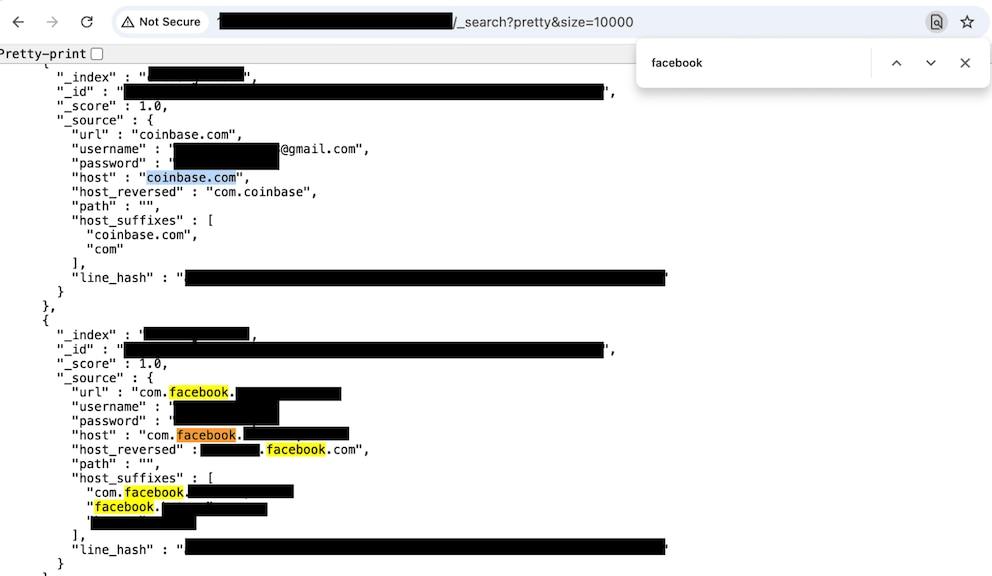
Fowler’s report explains that the database appeared to store information obtained through keylogging and “infostealer” malware: programs designed to silently extract credentials from infected devices.
Unlike other data sets analyzed by the researcher, it contained additional information, such as the “host_reversed” path in (com.example.user.machine) format, which made it easier to organize the stolen data according to victim and origin.
Fowler concludes: “This discovery also demonstrates that not even cybercriminals are immune to data breaches. The database was publicly accessible, allowing anyone who discovered it to potentially access the credentials of millions of people.”


